Games interaction with Web APIs, a horror story
Multiple vulnerabilities within a game server
Overview
I’ve worked in a games studio before and mostly the devs there were used to working within a closed system of the game binary and its assets, especially where the platform is console-based. Any online interaction was handled by a network programmer who essentially extended this closed system over to another closed system for the likes of PSN etc, But when interacting with in-house Web APIs a whole new world opens up as those same endpoints are available to external users.
Within one game I found unauthenticated raw SQL calls to an endpoint, directory indexing on this server showing more dangerous endpoints, backup files (ie text) for both code and data dumps, DLC contained in unauthenticated directories and just to top it all off a nice PHP backdoor left by someone who was there before me. A full list of issues will be summarised at the bottom of this post.
This was all done with very little effort, perhaps an hour every few weeks. There were potential avenues identified and unexplored because I was busy doing my OSCP at the time. This was also done on one server out of the many that the company controls. The company itself is well-established with games across pretty much every modern console and device.
The story
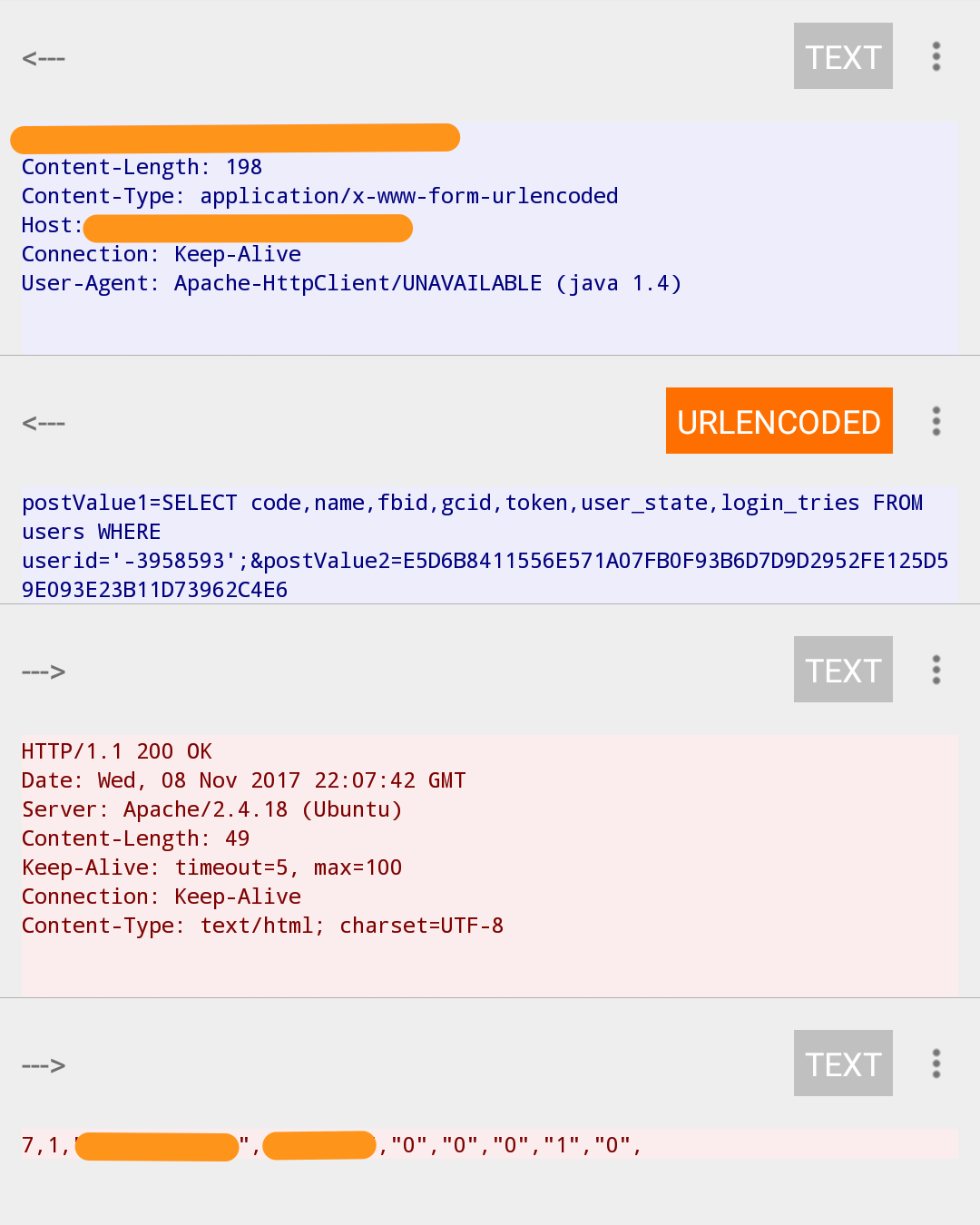
I like to briefly check new mobile apps to make sure they’re not sending away more than they need to. Usually nothing comes of it, but one call caught my eye and began this tale:
surely not?
I duplicated this request in curl and got the same result. postValue2 isn’t even required, so this is a completely unauthenticated request. I queried the information schema and got a list of tables so it was exactly what I feared. I previously couldn’t imagine that anyone would ever make this mistake.
Upon looking at a few more requests I noticed that entering an email address in the game’s login screen with any password would also return a username for that address if it existed before deciding if login was allowed or not.
Contacting the company
I contacted the company in question (anonymously at the beginning, but after months of contact and them being pleasant and very accommodating I removed the anonymity) and was told it would be passed to their QA team. I had to stress that this isn’t a bug; it’s working as intended but it’s still so very wrong and should be reimplemented by a developer from the ground up. As the game in question is on multiple platforms I at least suggested that commands are whitelisted until the patches could all be put out.
After a few weeks of trying to stress the importance of this with a non-technical member of staff, I’m told that a developer has eventually worked on it. I asked for permission to test this and was granted permission to test whatever I like.
So the fix worked against manual blind SQL injection but sqlmap got in within 2 minutes so we were back to stage one.
Whilst that was running I also took advantage of the carte-blanche I was offered and ran a dirbuster scan out of curiosity.
Directory fuzzing
Dirbuster showed me a lot of directories. None had any authentication against casual browsing, all had directory indexing enabled. This allowed me to find content for closed betas, the phpinfo file, all of the company’s DLC content and the original endpoint I was looking at, as well as similar ones with scary names like commandline.php
In case I ever forgot how to use curl there was a nice html form (named something obvious like testdb.html) which allowed me to type an sql command in there with an “Execute” button. In case I ever forgot SQL altogether, there were also .bak or .txt files of random live database dumps. Words fail me at this point. Backup text files of the php files present on the server were also there.
I contact the company and inform them of this too. A few more weeks go by with no progress so I keep emailing back asking for updates. Apparently the loss of business (paid DLC is already on various torrent sites) and the potential for fines and loss of reputation due to the easy access to their database wasn’t enough to spur them into frenzied action (I’d imagined a few developers would be ordering in pizza as sirens blared throughout the building after my reports). So I fire up nmap out of boredom and ran that.
nmap
A quick scan with nmap shows another http port open; 8080. It’s a default tomcat install and after nikto finds nothing useful, dirbuster works for quite a while and only gets one hit. Unfortunately this hit leads to a PHP backdoor written in Chinese. There was no obvious business reason for this port even being open, so I’m not entirely sure it was opened by the company themselves.
I contact the studio again, wrote a new report detailing all of the issues found to date and the words “Chinese Backdoor” seem to start the klaxons and the overtime and the pizza because everything was “addressed” a few days later.
The outcome
The reason I’ve not named the development studio in question yet is because a lot of the attempted fixes had a very narrow and literal focus. For example, If I wrote “directory indexing is enabled, e.g. for /x” with a screenshot, then the /x directory would have a blank index file, but every other directory was still affected. Port 8080 was closed which is good (but a brief nmap scan on another server shows it open there), but that SQL call looks like it was just converted to hex to try to obfuscate it. I’d been busy with my OSCP during this but now that that’s over I’ll attempt contact again and ask if they’d like their fixes verified.
Brief list of issues
-Directory listing enabled
-Raw unauthenticated SQL calls to endpoint
-Username enumeration from email address
-phpinfo file present
-HTTP port open for no reason
-HTTP ports have PUT method enabled
-PHP backdoor present
-DLC publicly viewable
-plaintext backups of database dumps and php files present
-Test html forms which interface with the server